Azure for AWS professionals - Networking - Azure - 06 Using Service Tags to define rules in NSGs
@20aman May 12, 2020In the Network Security Groups (or NSGs), if you want to define rules related to Azure Services e.g. allowing communication on a particular port to Azure Storage account. Then you can do so for each and every IP address published by Microsoft for Azure Storage service. This is a very cumbersome method and is not practical. Also, there is a limit to the number of rules you can write and the number of NSGs you can have in a subscription. You can have up to 1000 rules per NSG. Also, you can have only a maximum of 200 NSGs in a subscription. You can find these limits here: Azure subscription and service limits, quotas, and constraints.
Solution
Microsoft provides the capability to write NSG rules using Service Tag as a destination. When you leverage a Service tag the system ensures that it accounts for all the IP addresses for that service. Not only that, if any IP address changes or a new IP address is added then the Service Tag will account for that automatically. You can target whole services across different regions or services in a particular region. E.g. You can select Storage as a service or select "Storage.EastUS" to target the Storage service but only in the East US region.
Where is the Option
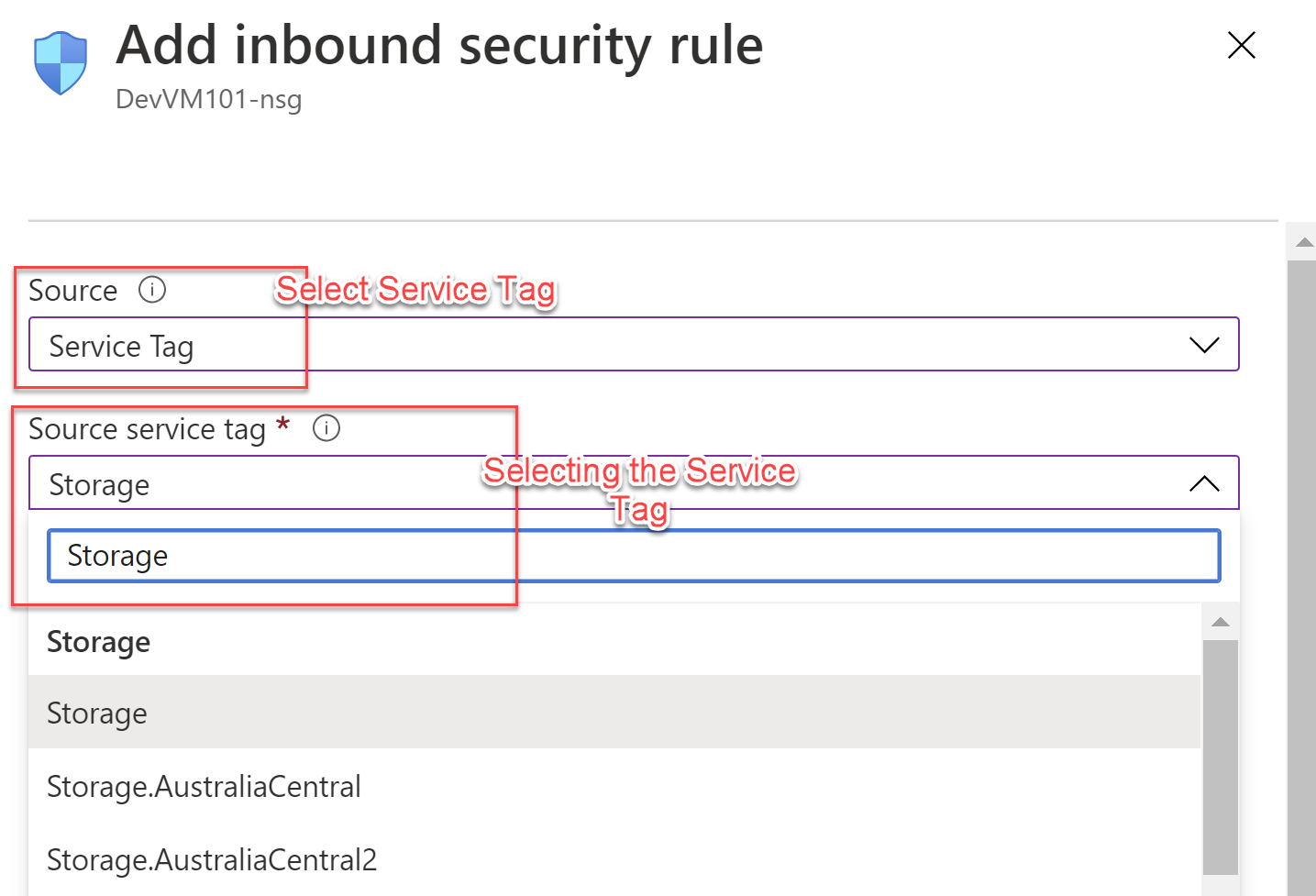
In the Inbound security rules, this option is available for the Source. In the Outbound security rules, this option is available for the Destination. Once you select the service tag as the option, then you are presented with a drop-down for the Service Tag selection. Internet is the default option for the Service Tag. You can type and search for the particular service tag e.g. Azure Storage, Azure Backup, etc.
You can read more about Service Tags here: Virtual network service tags.