Demystifying Azure Security - Azure SQL Database - Set Server Firewall
@20aman Mar 02, 2018This blog post is part of the Demystifying Azure Security series. All posts in the series can be found here: Demystifying Azure Security - Series Index
Azure SQL Databases have a powerful layer of security at the SQL Server level. This layer is provided by the SQL Server Firewall. Azure provides you granular control to configure this firewall and to manage who gets access to your Azure SQL Database. By default, everything is blocked by the firewall. If you want to get access to Azure SQL Database then you will have to configure the Firewall at the SQL Server level. Only the IP addresses you configure have access to the SQL Databases on the Server.
Another key point to understand is that once you configure a rule then because that rule is applied at the server level, it is applied to all the SQL Databases on that Server. So it is important to ensure that you segregate your databases on different SQL Servers if you don't want to share the access to those databases.
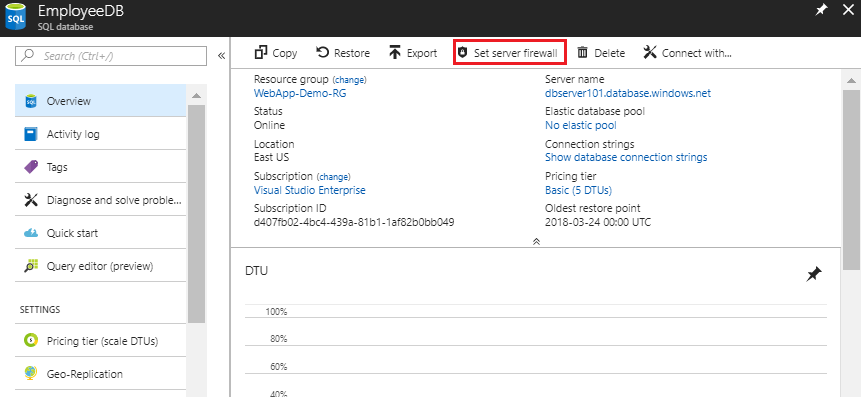
Accessing the Firewall Settings
You can access the firewall settings by navigating to your Azure SQL Database. Then at the top of the blade, you will find the option for "Set server firewall". Click on this button to access the firewall settings.
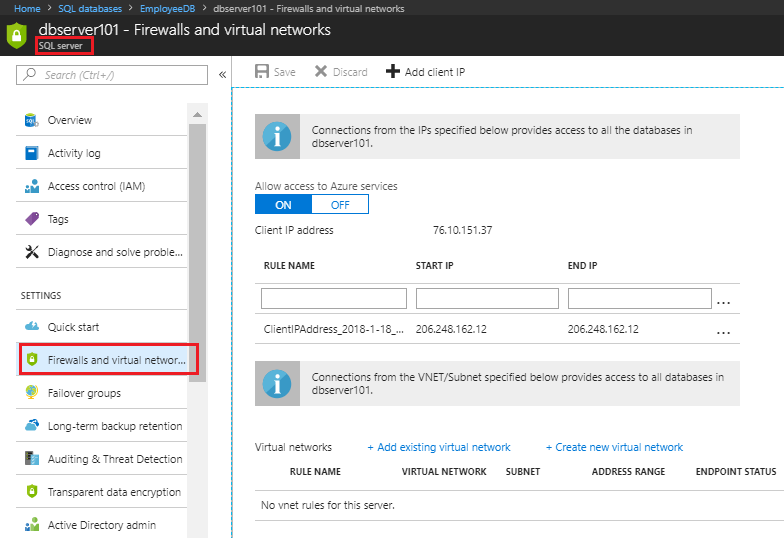
Another way to access the settings is on Azure SQL Servers. Navigate to the related Azure SQL Server for your database. Under the settings, find the option for "Firewalls and virtual networks". Clicking on this will also take you to the same firewall settings as the settings are set at the server level in both ways.
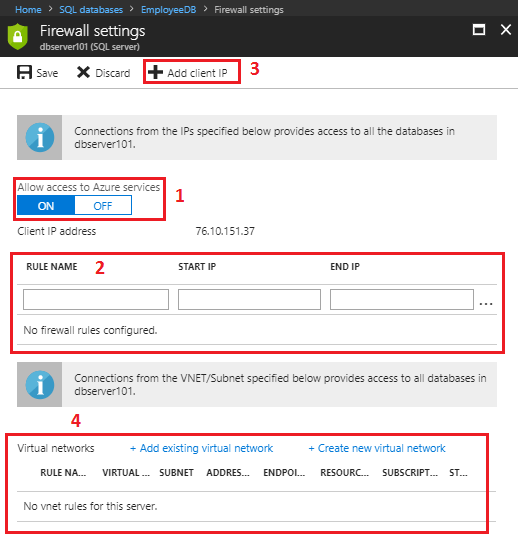
Firewall Rule Settings
Let us look at the firewall rule settings in more details.
- First, you have the option to enable or disable the access to Azure services as the toggle for "Allow access to Azure services". This is set to On by default when creating the Database and SQL server. You can disable it here. This option allows Azure services to provide monitoring data and recommend changes at the database level.
- Second, you have the option to configure a Rule. This is where you configure which IP Addresses have access to the SQL Server.
- One commonly used Rule is to open the access for Client IP. This is the IP address of the machine from where you are connected to the Azure Portal. This is provided for the common scenario where you want to connect and access the SQL database via SSMS (i.e. SQL Server Management Studio) or by any other way from your development box. There is a button to simply add the rule for allowing Client IP by clicking on "+Add client IP". The client IP is also authomatically displayed under the "Allow access to Azure services" section
- Lastly, there is an option to allow access to the SQL databases from a particular Subnet in a Virtual Network in Azure, without having to manually configure their IP addresses. This feature requires Service Endpoints to be configured at the Virtual Network level. We will discuss this feature in a later blog.
A typical Rule contains:
- A Rule Name - which could be any descriptive name for the rule. E.g. it could be name of the single VM for which you want to configure the access or it could be name of the network for which you are opening the access
- Start IP - Start of the IP address range for which you want to open the access. E.g. if you want to open access for 10.20.1.0/24 then the Start IP will be 10.20.1.0
- End IP - End of the IP address range for which you want to open the access. E.g. if you want to open access for 10.20.1.0/24 then the End IP will be 10.20.1.255
Note: If you want to provide access to only one IP address then provide that IP address for both Start and End IP fields.
Note in the image below that:
- The client IP rule was added by clicking on the "+Client IP" button. Note that the Start and End IP are same for this rule
- Second is a custom rule which allows access to the SQL Server from a specific VM hosting Website (which will need access to the database)
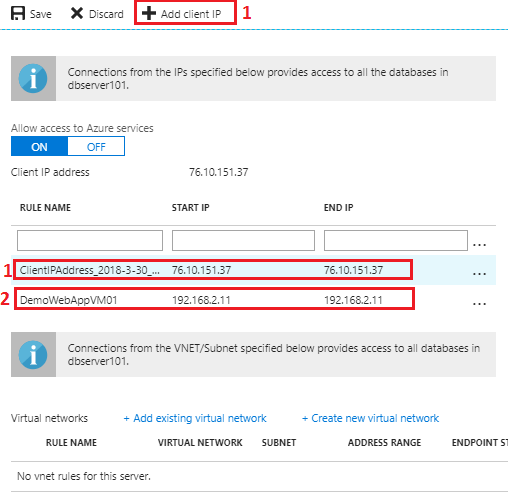
Once you are done configuring, just hit Save to apply the firewall rules.
Next, we will learn about setting up the Firewall Rule for Virtual Networks and also Service Endpoints for Azure SQL on Virtual Network